 By Aaron Kesel
By Aaron Kesel
Rogue unknown cell-site simulators are being actively used in Washington, D.C., Maryland and Northern Virginia according to News4 I-Team who worked with a mobile security expert to determine the usage of the devices.
Last month, the U.S. Department of Homeland Security said it had seen activity in Washington, D.C., of what appear to be rogue surveillance devices that could be used to hijack cellphones, listen to calls and read texts. The devices are otherwise known as International Mobile Subscriber Identity (IMSI) catchers or stingrays, NPR reported.
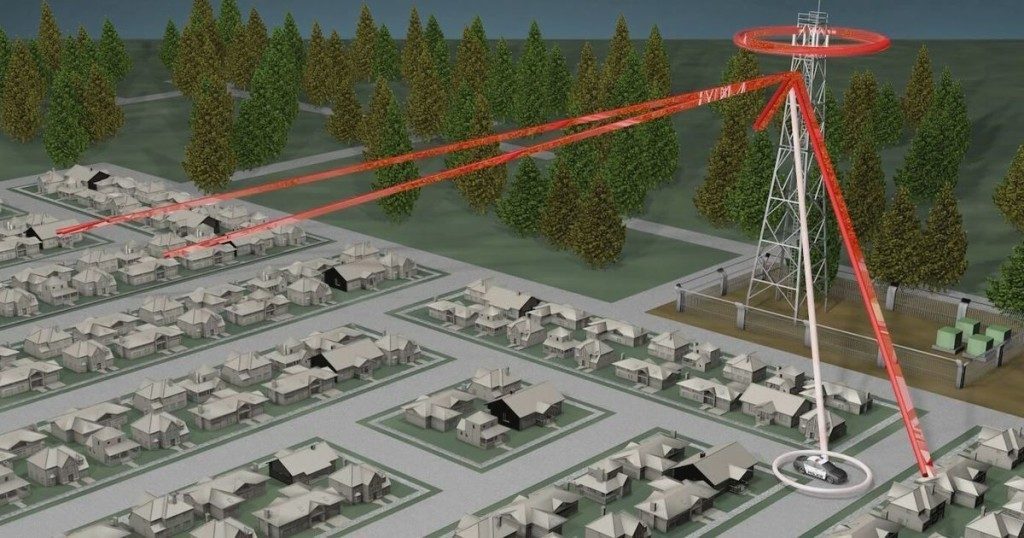
The devices work by tricking mobile devices within a determined radius into connecting onto them instead of legitimate cell towers, revealing the exact location of a cellphone. More sophisticated versions of the device can even eavesdrop and intercept calls by forcing phones to use 2G wireless technology. Some even attempt to plant malware on the devices that are being targeted.
The devices can be mounted in vehicles, drones, helicopters, and airplanes, allowing police to gain highly specific information on the location of any individual phone, down to a particular apartment complex or hotel room. But where police can use them, so can anyone else with knowledge to build them or where to buy them.
IMSI catchers can cost anywhere from $1,000 to around $200,000. They are the size of a small briefcase; some are as even as shockingly small as a cellphone. However, according to the EFF, “anyone with the skill level of a hobbyist can now build their own passive IMSI catcher for as little as $7 or an active cell-site simulator for around $1000.”
The agency added that it believes “the malicious use of IMSI catchers is a real and growing risk.” Senator Ron Wyden wrote to DHS asking for information about the use of IMSI catchers by foreign intelligence agencies.
DHS has warned rogue devices could prevent connected phones from making 911 calls, saying, “If this type of attack occurs during an emergency, it could prevent victims from receiving assistance.”
D.C. Councilwoman Mary Cheh said that the spy technology should be a concern for all who live and work in the District.
The I-Team’s test phones detected an absurd 40 potential locations where the spy devices could be operating while driving around for just mere hours.
The DHS hasn’t disclosed how many IMSI catchers it found or where those “rogue surveillance devices” were detected. The agency also said it did not determine who was operating them.
According to NBC the devices are operating in Langley, the Pentagon and Fort Myer to name a few places where they were found.
Although NBC tries to dismiss the devices as “rogue technology,” stating they are likely used by law enforcement, it’s worth noting the DHS has stated previously they don’t know who is operating this tech.
“The good news is about half the devices the I-Team found were likely law enforcement investigating crimes or our government using the devices defensively to identify certain cellphone numbers as they approach important locations,” Aaron Turner a mobile security expert, said.
Further, even if the technology was used by law enforcement, its usage is violating privacy and is illegal without a warrant as it scoops up all the data collected by cell phones in the area without discrimination; which violates constitutional protections, according to the EFF. And what if it’s being run by a rogue police force, like the one that operated at Norfolk, Virginia, Naval Shipyard for 12 long years before being caught, as Activist Post reported on?
DHS acting undersecretary, Christopher Krebs, the top official in the National Protection and Programs Directorate, noted in a response letter to Wyden that the DHS lacks the equipment and funding to detect Stingrays even though their use by foreign governments “may threaten U.S. national and economic security.”
Krebs wrote, “Use of IMSI catchers by malicious actors to track and monitor cellular users is unlawful and threatens the security of communications, resulting in safety, economic, and privacy risks. … Overall, DHS’s National Protection and Programs Directorate believes the malicious use of IMSI catchers is a real and growing risk.” The agency added that NPPD “has observed anomalous activity in the Nation Capital Region that appears to be consistent with IMSI catchers. NPPD has not validated or attributed such activity to specific entities or devices.”
After the DHS admission, three House members sent a letter to the Federal Communications Commission, demanding that the FCC “take immediate action under federal law to address the prevalence of what could be hostile, foreign cell-site simulators—or stingrays—surveilling Americans in the nation’s Capital.”
Last month, Senators. Cory Gardner (R-Colo.), Ron Wyden (D-Ore.), Rand Paul (R-Ky.) and Ed Markey (D-Mass.) called on the DHS to release an unclassified PowerPoint presentation detailing the threat, The Hill reported.
The presentation was given by a DHS official at the Federal Mobile Technology Forum in Mclean, Va., in February, according to the four lawmakers.
The PowerPoint presentation was described as “detailed,” but gave no other information about what it may reveal.
“The American people have a legitimate interest in understanding the extent to which U.S. telephone networks are vulnerable to surveillance and are being actively exploited by hostile actors,” they wrote in a letter to DHS official Christopher Krebs.
The EFF states that the “problem is law enforcement and the intelligence community would surely agree that these technologies are dangerous in the wrong hands, but there is no way to stop criminals and terrorists from using these technologies without also closing the same security flaws that law enforcement uses.”
In that respect, that means in order to stop rogue potential criminal activity the security flaws would have to be fixed and the holes patched; but if that’s done, then law enforcement wouldn’t be able to use it either. This reporter must be the only one who is okay with that?
Aaron Kesel writes for Activist Post. Support us at Patreon for as little as $1 per month. Follow us on Facebook, Twitter, Steemit, and BitChute. Ready for solutions? Subscribe to our premium newsletter Counter Markets.

since all are illegal, even if operated by the government, there appears to be no reason why a citizen cannot destroy the device when he or she encounters it